
: Access Intelligence
An autonomous, intelligent system of engagement for better access governance. Humans, Agents or Machines – explain every access control decision and facilitate remediation and healing at scale
Access Governance:
The Tenability conundrum
Enterprises spend vast sums each year on access governance and identity
management, yet data breaches remain widespread, with human error and outdated permissions cited as persistent root causes. According to the Verizon Data Breach Investigations report, system intrusion led breaches had increased, from 36% in 2024 to 53% in 2025, in terms of incidence.
Decaying Access Models
Incomplete or obsolete access and role data weakens security models rapidly, forcing enterprises into expensive, reactive remediation cycles.
Skyrocketing risk
Broad ranging permission models lead to a wider blast radius in the event of breaches.
The Agentic Enterprise
The explosion of agentic and non-human identities are further likely to compound the problem.
The Solution: The Enterprise Knowledge Graph
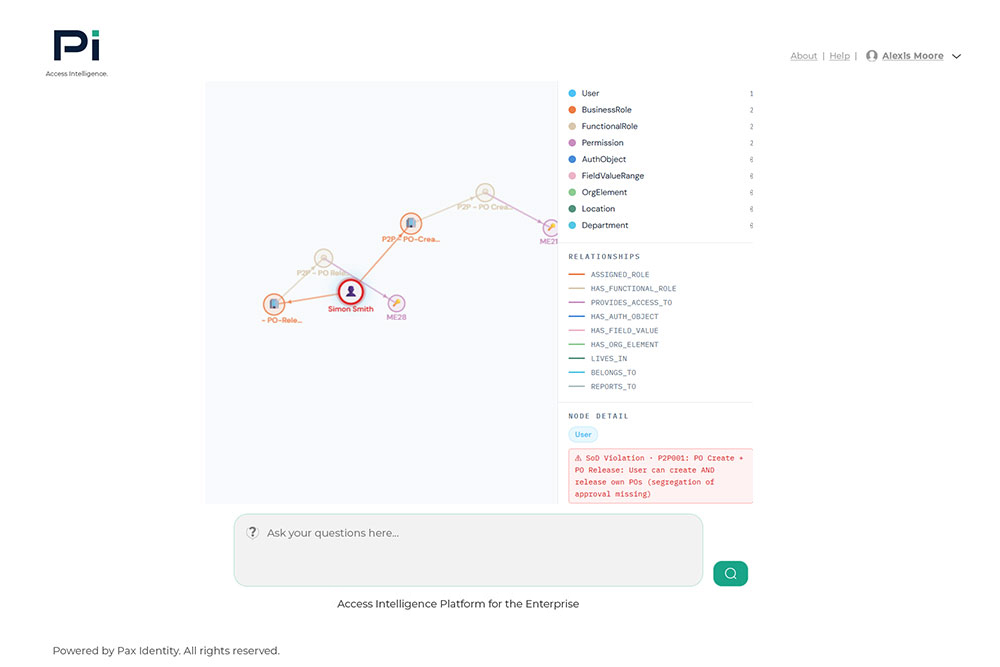
Pi moves beyond automated workflows to autonomous intelligence. At our core is a dynamic Knowledge Graph—built through machine learning and neural networks—that forms a living view of your entire access environment.
Core Capabilities
- Continuous Learning: Unlike static systems, Pi interrogates and refines permission sets, cleansing inaccuracies through predictive approaches.
- Self-Healing Remediation: Pi proactively identifies vulnerabilities and proposes target fixes, reducing remediation timelines from years to weeks.
- Impact Modeling: Assess how organizational or process changes will affect your application role models before you commit to them.
- Actionable Intelligence: Transform raw permissions data into a living system of record that delivers a measurable ROI as it evolves.
Access Intelligence for everyone within the enterprise
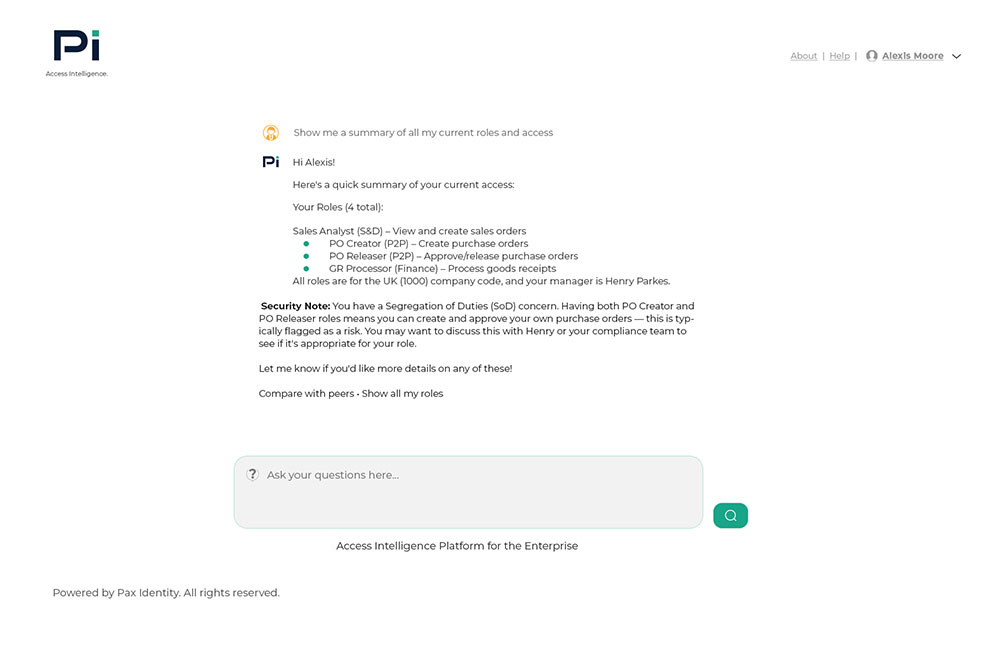
- NLP Interface: Your next request for access can be queried through Pi. The solution will tell
you all about what you require and any additional context-based questions in natural text. - As easy as chat: Ask the Pi intelligent agent through Microsoft Teams or your enterprise
chat platform any question related to access, segregation of duty risks, role compositions
or specific access events. It will tell you what you need to know. - Identify, Manage and Remediate risks: The knowledge graph-based interface shows
relationships, outliers and root causes of conflicts in plain text that allows you users to
feed credible inputs for remediation of rogue or misconfigured access, in the real time.
Seamless Integration with Your Ecosystem
Pi acts as the intelligent layer above your existing Foundational Plane (Active Directory, Azure AD, Workday) and Systems of Record.
Enterprise Applications
Governance & Fulfilment
SAP, Microsoft Dynamics 365
ServiceNow
Salesforce, Coupa
Saviynt
Snowflake
SailPoint
Ready to turn intention into action?
Take a decisive step towards building intelligent and autonomous access governance solution that will seamlessly adapt to your current Identity platforms while significantly enhancing your preparedness for the agentic enterprise.
